Accurate Caller Investigation of 0120427540 With Trusted Overview
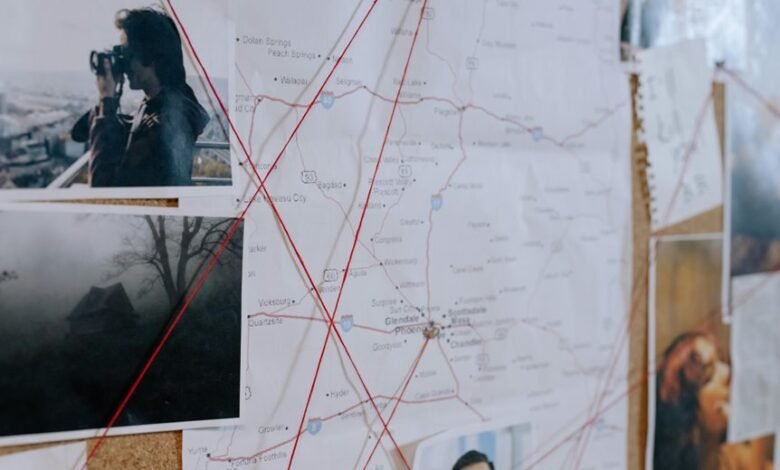
Accurate caller investigation of 0120427540 requires a transparent, privacy-conscious lens and verifiable signals. The approach emphasizes identity verification, access audit trails, and independent corroboration to assess risk without compromising user privacy. It balances alert mechanisms and official source validation with clear flagging of inconsistencies, atypical channels, or dubious consent logs. Structured notes, metadata cross-checks, and reproducible conclusions underpin the process, inviting scrutiny while maintaining safeguards. The outcome hinges on trustworthy sources that prompt further examination.
What 0120427540 Is Warning You About
The number 0120427540 has been observed issuing warnings that suggest potential concerns about security and privacy.
The first idea centers on data handling transparency, urging stakeholders to audit access trails and consent logs.
The second idea emphasizes proactive risk assessment, advocating independent verification of caller identity and alerting mechanisms.
How to Verify a Caller Without Breaching Privacy
To verify a caller without compromising privacy, a structured approach prioritizes verifiable signals over intrusive data collection. The method emphasizes transparency, consent, and minimal data handling, aligning with privacy basics.
Verification relies on corroborated identifiers, behavioral patterns, and official signals. This objective process supports informed judgments, fostering trust while preserving autonomy through disciplined, non-invasive caller verification techniques.
Red Flags and Trusted Sources for Caller Legitimacy
Red flags in caller legitimacy can be identified through a concise, evidence-based framework that emphasizes anomaly detection and source validation. The analysis notes patterns, such as inconsistent identifiers, suspicious timing, and atypical contact channels. Trusted sources include official registries and verified contact databases. Privacy caution and verification tactics remain essential, balancing transparency with data protection and minimizing exposure to manipulated information.
Step-by-Step Framework for Accurate Caller Investigation
A step-by-step framework for accurate caller investigation employs a disciplined sequence of verification, documentation, and assessment to minimize uncertainty. The process emphasizes methodical data collection, corroboration across sources, and objective evaluation. Distance from bias supports reproducibility, while structured notes enable traceability. Core actions include caller investigation, verification techniques, cross-checking metadata, and documenting rationales to facilitate transparent, terminable conclusions without unwarranted assumptions.
Conclusion
The investigation of 0120427540 is grounded in verifiable signals, consented access logs, and independent corroboration. By cross-checking metadata, validating official sources, and flagging inconsistencies, the analysis remains objective and privacy-conscious. A transparent audit trail serves as the backbone, while alert mechanisms and red-flag indicators guide risk assessment. The process proceeds like a measured clock: each identified datapoint ticks toward reproducible conclusions, ensuring reliability without compromising individual privacy.




